
Should Homeland Security Have a ‘Bug Bounty’ Program for Fixing Cyber Vulnerabilities? (H.R. 3710)
Do you support or oppose this bill?
What is H.R. 3710?
(Updated October 23, 2019)
This bill — the Cybersecurity Vulnerability Remediation Act — would authorize the Dept. of Homeland Security (DHS) to disseminate information to the public about vulnerabilities in the software and hardware of information systems. It would also authorize DHS to establish an award program (also known as a bug bounty program) to encourage independent researchers to identify and report vulnerabilities and solutions for those vulnerabilities to the department.
Additionally, this bill would direct DHS’ Cybersecurity and Infrastructure Security Agency (CISA) Director to provide a report to the House Homeland Security Committee and Senate Governmental Affairs Committee on how the agency carries out its responsibility to coordinate vulnerability disclosures, disseminate actionable protocols to mitigate cybersecurity vulnerabilities, and how the agency plans to improve information provision policies.
Argument in favor
Bug bounty programs are a quick, effective way to find and fix IT vulnerabilities. The success the military and Dept. of Defense (DOD) have seen from these programs is a good argument for implementing a bug bounty program at DHS. Additionally, even if DHS is already carrying out most of the responsibilities in this bill, it’s still worth codifying the agency’s responsibility to disseminate information about hardware and software vulnerabilities to the public.
Argument opposed
Bug bounty programs are expensive and cumbersome to maintain. Their costs are also unpredictable, as it’s impossible to estimate how many bugs will be found and what the payouts will be. They also aren’t a substitute for internal cybersecurity capacity. This bill also only allows generic disclosures, so it’s unlikely to be effective.
Impact
Technology users; software and hardware vulnerabilities; DHS; Congress; and DHS’ Cybersecurity and Infrastructure Security Agency (CISA) Director
Cost of H.R. 3710
The CBO estimates that implementing this bill would cost $44 million over the 2019-2023 period.
Additional Info
In-Depth: Rep. Sheila Jackson Lee (D-TX) introduced this bill to authorize the Dept. of Homeland Security (DHS) to disseminate information about software and hardware vulnerabilities to the public and establish a bounty program for those who identify and report vulnerabilities to the agency.
Deborah Chang, Vice President of Business Development and Policy at HackerOne, contends that hackers have “unique insights” to offer to the federal government:
“With no clear solution to the increasing threats to cybersecurity, the United States must enlist the help of hackers. Hackers have unique insights. They have diverse skill sets and expertise. And, there are a lot of them ready to help. They are good at building things, but importantly, they also enjoy breaking them. Different from the bad guys, they want to break things in order to have them fixed. To fully leverage the power of hackers, it’s important that they aren’t penalized for the work they do, and that the vulnerabilities they find are acknowledged, analyzed and eventually fixed.”
Chang argues that a bug bounty program is the best way for DHS to work with hackers. To prove bug bounty programs’ effectiveness, she points to the Dept. of Defense’s (DOD) work with hackers, which has resolved over 5,000 security vulnerabilities since 2016. Hackers work quickly, too. For example, Hack the Pentagon’s bug bounty program’s first submission was reported within 13 minutes of the launch; and over 130 bugs were resolved in the Pentagon’s systems by the end of the launch month.
Patrick Coyle, a freelance writer dealing with chemical security and safety issues, contends that this bill as written doesn’t work. In a post on his personal blog, he writes:
“[A]ny mitigation measures that the Cybersecurity and Infrastructure Security Agency publishes as a result of this bill will have to be limited to the generic measures that CISA already includes in the control system security advisories published by NCCIC-ICS. CISA is not going to be able to publish any true ‘hacks’ of the affected software or firmware because of these issues and the bill would do nothing to provide liability protection for owners or users that would use such ‘hacks’ even if reported by CISA… [As is,] we have Congress taking action to solve a cybersecurity action that is really no action at all. There is a potential (but very unlikely) way for the House to correct this bill, even under the suspension of the rules process. Under a motion to reconsider after passage, the bill could be sent back to the Homeland Security Committee with direction to offer an amendment…. I do not really expect that this would happen, but I can always be surprised by congresscritters. More likely such changes would have to be undertake in the Senate Homeland Security Committee if/when they markup HR 3710 after it passes in the House, but before it is considered under the unanimous consent process in the Senate. Again, I would not really expect that to happen.”
Katie Moussouris, a bug bounty expert and founder of Luta Security who helped the Pentagon set up its bug bounty program, argues that rather than setting up a bug bounty program, Congress “should be funding an overhaul of internal capabilities” at federal agencies to make them more secure, rather than relying on bug bounties to replace internal capabilities:
“Bug bounties should only be used in circumstances where you’ve done your best to find and fix issues yourself, not as a replacement for due diligence and process, and not as a replacement for professional penetration testing.”
This legislation unanimously passed the House Homeland Security Committee with the support of two Democratic cosponsors.
Of Note: DHS is already performing many of the cybersecurity activities this bill would authorize. The department has several programs providing services and information to help system administrators, software manufacturers, and the general public identify cyber vulnerabilities. For example, the DHS Common Vulnerabilities and Exposures program helps software vendors identify risks and communicate to their customers how vulnerabilities affect their products and services.
Bug bounty programs have become very popular with military services and the Dept. of Defense. They’ve also proven fairly effective: in early August 2019, the Air Force announced that its latest bounty, in which it partnered with third-party firm Bugcrowd to invite white hat hackers to find flaws in its new cloud system, the Common Computing Environment, revealed 54 flaws.
Media:
-
House Homeland Security Committee Report
-
CBO Cost Estimate
-
Chemical Facility Security News Blog (Opposed)
-
FedScoop
-
FedScoop (Context)
Summary by Lorelei Yang
(Photo Credit: iStockphoto.com / katleho Seisa)The Latest
-
 IT: 🛢️ New Vermont measure could charge Big Oil for climate damages, and... Do you think Trump is guilty?Welcome to Friday, May 10th, friends... Vermont could be one of the first states to hold Big Oil accountable for the damages read more...
IT: 🛢️ New Vermont measure could charge Big Oil for climate damages, and... Do you think Trump is guilty?Welcome to Friday, May 10th, friends... Vermont could be one of the first states to hold Big Oil accountable for the damages read more... -
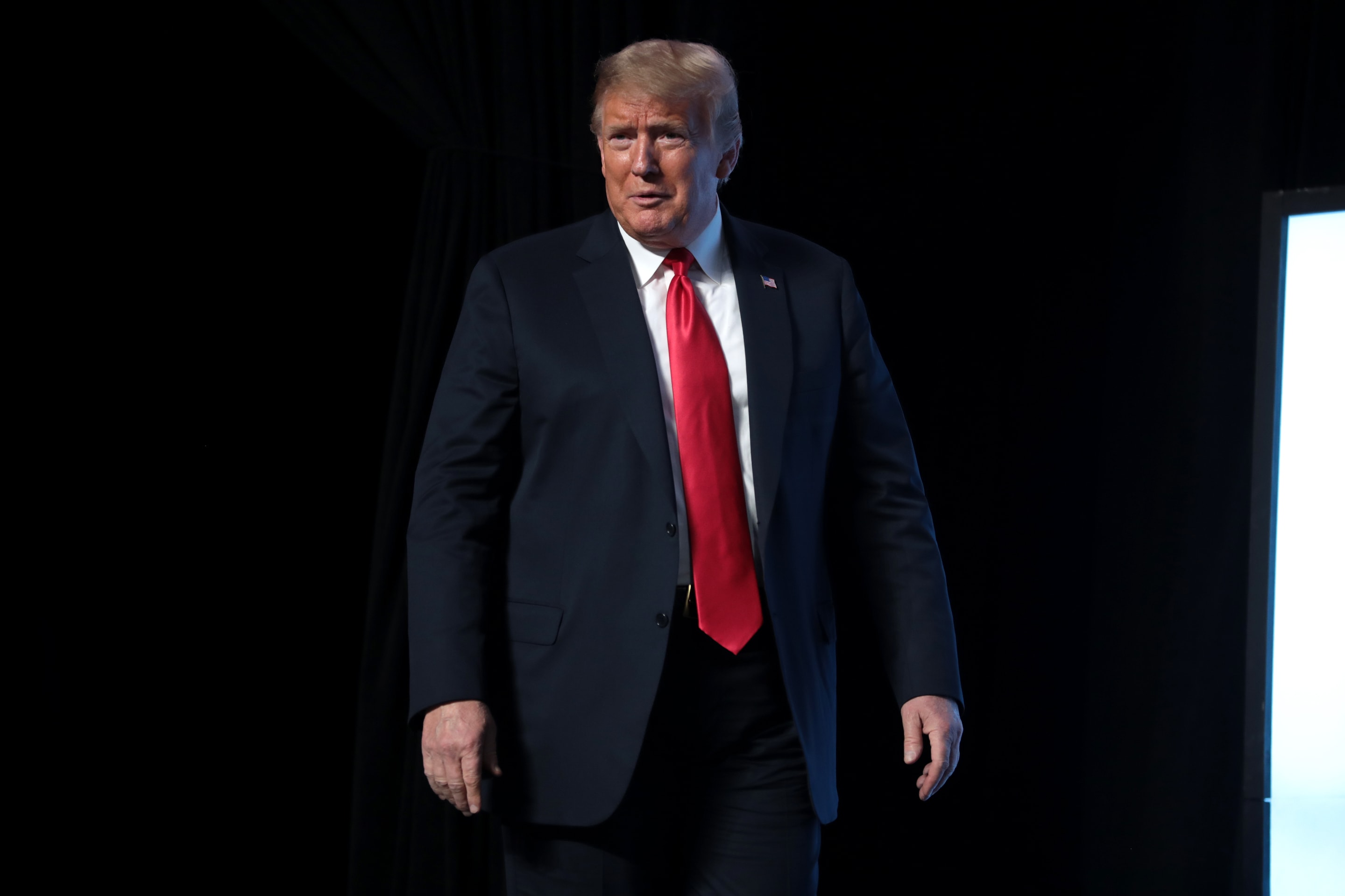 Stormy Daniels Takes the Stand in Trump Hush Money TrialUpdated May 9, 2024, 5:00 p.m. EST Adult film star Stormy Daniels, also known as Stephanie Clifford, spent two days on the stand read more... Law Enforcement
Stormy Daniels Takes the Stand in Trump Hush Money TrialUpdated May 9, 2024, 5:00 p.m. EST Adult film star Stormy Daniels, also known as Stephanie Clifford, spent two days on the stand read more... Law Enforcement -
 Vermont Measure to Charge Big Oil for Climate DamagesWhat’s the story? Vermont is expected to become one of the first states to hold Big Oil accountable for the damages caused by read more... Environment
Vermont Measure to Charge Big Oil for Climate DamagesWhat’s the story? Vermont is expected to become one of the first states to hold Big Oil accountable for the damages caused by read more... Environment -
 IT: Trump's 2016 'deny, deny, deny' campaign strategy, and... How can you help the civilians of Ukraine?Welcome to Wednesday, May 8th, weekenders... As Trump's hush money trial enters it's third week, the 2016 campaign strategy of read more...
IT: Trump's 2016 'deny, deny, deny' campaign strategy, and... How can you help the civilians of Ukraine?Welcome to Wednesday, May 8th, weekenders... As Trump's hush money trial enters it's third week, the 2016 campaign strategy of read more...
 Climate & Consumption
Climate & Consumption
 Health & Hunger
Health & Hunger
 Politics & Policy
Politics & Policy
 Safety & Security
Safety & Security
